Proof of Capacity
Proof-of-Capacity (PoC) is a consensus mechanism based on providing a proof of storage space. In a PoC consensus algorithm, when a node submits a block to the network it must also provide a valid proof of capacity. It is very difficult for a node to generate a valid capacity proof without having the corresponding storage size, and the proof can be verified by any node in the network. If both the block data and the proof are valid, the block will be accepted by the rest of the network. The basic principle behind how a proof is provided is as follows: during the initialisation phase, a series of data is generated according to the protocol and is saved in the storage devicecapacity. When the a new block is to be generated, a part of this stored data is revealed retrieved based on the value of a random number. This data part is then used to generate a proof and the node is able to compete for the next block.
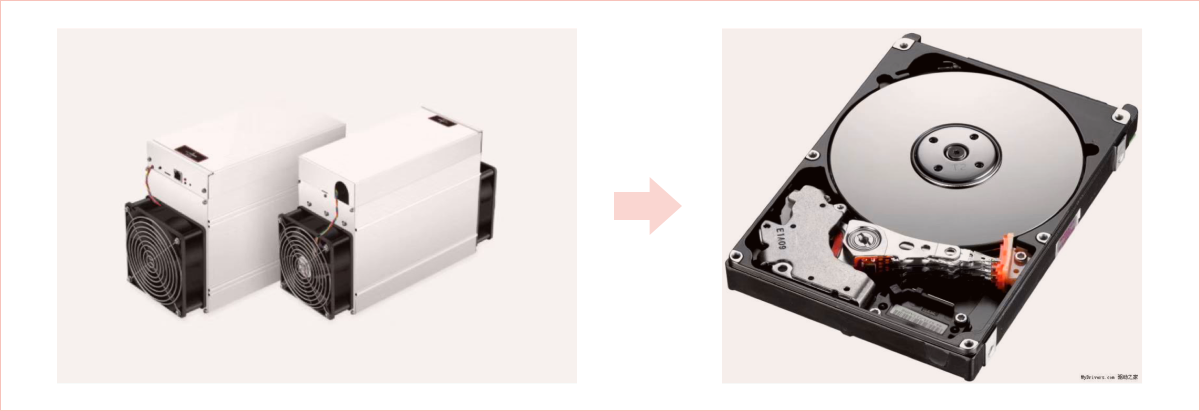
The MASS PoC protocol and bitcoin’s Nakamoto consensus protocol can both be described with a unified mathematical model. is a one-way permutation function for space to space . The verifier takes a value y from space , and within a certain period of time, the prover must submit give a corresponding value x for in space within a certain period of time so that where . The Nakamoto consensus protocol uses an exhaustive brute-force search method to calculate values with by iterating all possible value in order to find the right when a collision of happens, making multiple requests on the function to find the corresponding value and thereby confirm the value of . On the other hand, the MASS PoC protocol uses a look-up table method, first performing an offline analysis and recording all the values that correspond with , and then when solving for simply looking up the corresponding value when finding a . Despite the difference in methods, in terms of security the MASS and Nakamoto consensus protocols are very similar within regards to algorithm security.